Alex Mwai
Alex is a geek, like total geek. Paranoid like all geeks in cyber, Courageous, Protector, Learner, Passionate over tech, Loves Pop Culture, Socially awkward and Loving.
Lebanese National, Kenyan Father.
She is Loving, Heartful, full of life, Warm, Delightful to be around, Remorseful probably after a huge loss, Challenging, Bright, Poetic and a Forgiver.
Everything goes berserk after her boyfriend is killed in the streets of Nairobi. Then an Disinformation campaign follows to deceive the public and law enforcement so that no one finds the real reason behind that hit.
Having attained several cyber skills, Vanessa goes for the hunt to find who wants her dead and how they got to Alex.
Alex is a geek, like total geek. Paranoid like all geeks in cyber, Courageous, Protector, Learner, Passionate over tech, Loves Pop Culture, Socially awkward and Loving.
Raphael Letui is the son of a senior officer, The Assistant Director at the Directorate of Criminal Investigations. Due to mistrust in the service, his father and him run several off-book operations to recruit Confidential Informers via their Family Security company after several of their Assets get killed, due to either corruption or rookie Asset-Handling during operations. Letui is Forceful, Boastful, Wealthy, a Protector, Respectful, Determined, Courageous and Patriotic.
This is the intelligence branch of Al Shabab. You can tell they are running operations in the desert with some Al-Qaida individuals on the Books Prologue.
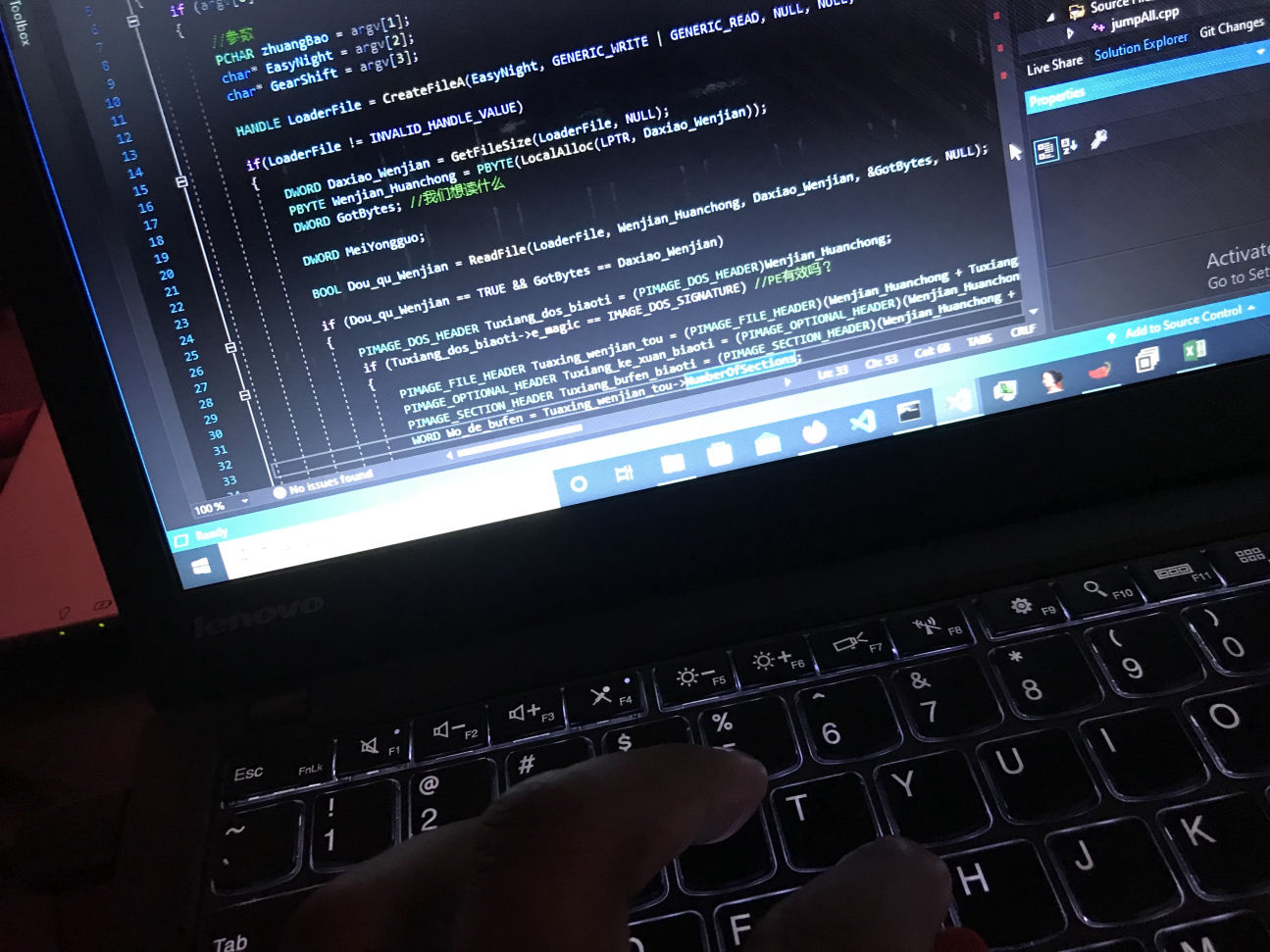
YaToosh is the implant Vanessa is using to spy on an individual in a Safehouse. It is modular but lacks the secure webcam delivery. When targeting bad guys, we usually have to run operations in a secure way for covert collection of Intelligence. However, in some operations, a target does not know if he is being observed. YaToosh is Hebrew for Mosquito. Its explained well in the other chapters.
This is a fully fledged backdoor with extended modularity that is used on clandestine collection for Signals Intelligence on an endpoint. It’s explained further on the coming chapters.
This is operational security. It is part of a study known as Information Operations, which is like an upgrade of Information Security to cyber.
This is a service on a webserver over TOR. It’s explained well on the chapters, I don’t wonna mess the story so, continue reading. You will get to it.
This is a language from the C Family. It’s used to write software for Apple devices. It works well with Swift as in Swift is made from Objective-C to make it easier for engineers to make apps for Apple more faster.
This is Component Object Model, which was earlier known as Object Linking and Embedding, OLE. Some of the important terms when studying COM are: a)COM OBJECT – This is the instance of a COM class. b)COM CLASS – This is an implementation of one or more COM interfaces. c)COM INTERFACE – This goes to binary contract consisting of methods with a binary layout. d)COM COMPONENT or SERVER – a deployed asset from COM consisting of the COM Classes. In the book you will see Vanessa playing with CoCreateInstance and others which we use when working with COM.
This function creates and initializes a single object of the class associated with Class Identification. In the book Vanessa uses it this way: CoCreateInstance (CLSID_SystemDeviceEnum, 0, CLSCTX_INPROC, IID_ICreateDevEnum, (void**)&create_dev)
This is a structure, which contains the information required for dimensions and color format of the webcam shot, as Vanessa accessed it from the devices during the stream webcam-shots. This structure can be found on the GDI documentation on MSDN. MSDN is Microsoft Development Network.
When writing C/C++ we usually load headers, which come with an extension of dot H. These files sometimes will bundle with the Software Development Kit (SDK) depending on what you are developing on and require. Now, dshow.h is a header we use when working with DirectShow Applications. It will use the static libraries like Strmiid.lib and Quartz.lib for linking and lib dependencies. In the book, Vanessa imports the header like below: #include dshow.h with the greater than and lesser than markers/symbols like when loading Windows.h.
This places a library-search record in the object file, telling the linker to add the library to the list of library dependencies, as if you added it in the project properties. Vanessa adds the pragma as below: #pragma comment(lib, “strmiids.lib”) #pragma comment(lib, “strmbase.lib”)
This function does initialize the COM library on the current thread and it identifies the model for STA, which means Single Thread Apartment. Vanessa uses it before calling CoCreateInstance as below: CoInitialize(0); Zero is always the reserved one and must be Zero or NULL when initiated. Vanessa and Alex make jokes about STA in coming chapters.
This function retrieves the class object from a DLL Object handler or object application. If this function were called outside the loader lock, Vanessa would be able to manipulate some security issues on the target computer.