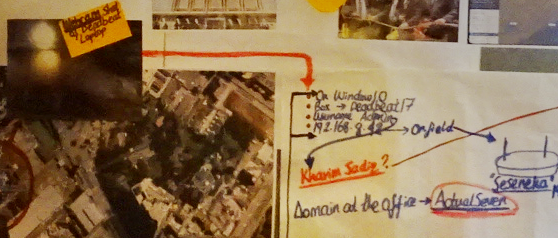
This is the webcam view of the safehouse after the first Webcam shot, that warms up the camera. Vanessa had it on her operations wall. Vanessa has already exploited the Windows 10 laptop known as Deadbeat17. She has already tracked the actor behind the keyboard as Kharim Sadiq
The operator can do more shots, depending on the implant's conditions and the intelligence collection per target.
In most operations, the actor behind the exercise will want to stream without having a LED light go on the target's PC. These needs are mostly objectives and requirements i have seen requested during Counter Terrorism (CT) ops.
As the book opens on the introduction chapter,
we see Vanessa has already gained access to an Outpost or a Safehouse,
by NISA agents who are actually conducting offensive covert operations in Nairobi.
In real life they do and so do others.
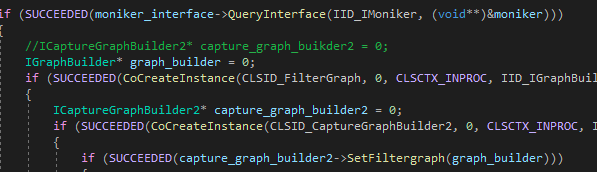
At some point she was using C/C++ to emulate and stream web camera data like shown below:
She eventually switches over to an Implant they had used before, that they codenamed YaToosh in the book.
We gotta appreciate that every Nation spies on another, overtly and covertly.
On the last chapters,
Vanessa maliciously gains control of the machine that one of the NISA
agents is using on a building near Karuna road to brute force into sshd service of a Linux server.
The Linux server is actually the Dark web that Vanessa,
Alex and Ibrahim used to communicate, deconflict and then
plan for Offensive Cyber Operations (OCO) against Somalia.
From the story as the book continues, we can see the reasons why they had to go for Somalian government.
They were just hactivists. But they had a message for that particular hack and leak operation.
But on the current op, her main luck was that she gained access to that machine that was brute forcing
their server
and it was one of the adversarial actors in the field, who stupidly used a windows laptop.
Now, any operator out there who has gone for a close-access or a close-net op, knows that you don’t
use Windows Box on a such an OCO operation.
It’s quite risky, and being owned by the adversary could happen.
And it did in this story.
Usually, if you are running a covert operation in the field,
you will need to go back to the office or a Safehouse depending on the op,
either for debriefing or further exploitation.
And that’s how Vanessa owns the network in that Safehouse.
In the last chapters,
the hack is more in detail because we see the NISA actors
learning about the ATPU asset who has penetrated them and is inside their walls.
With a good implant,
Vanessa just like any other cyber actor can travel laterally inside the Safehouse computers.
And that’s how she learns who is after her,
and who is next on their target list.
She is able to travel through the endpoints and collect files from each hard drive,
then activate webcam collection and literally see the Somalian who fired at her that night.
That’s right, the one who shot at her when she arrived at Alex’s.
She is able to activate microphones on the Safehouse operational laptops.
Though we don’t know if she hands all that collected intel to Inspector Letui,
we can see that she does call him on WhatsApp to warn him about Aisha.
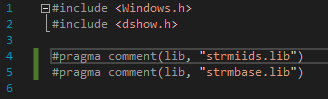
The application she is working on to get the webcam stream, is on C/C++ and also she is messing
around with COM. From the book she imports some libs as shown below, as she gets the structures done:
NISA is National Intelligence and Security Agency of Somalia, headquartered in Mogadishu.
The agency is known for its brute-force operations against Al Shabab in the capital.
I hope you enjoyed the seven free chapters online.
There is a lot of editing ongoing. So some chapters, even those online are changing before
the release date of the full book.
The Confederate is coming out soon, on both Paperback and Kindle.